Cloud-Based Remote Monitoring
The RemoteIQ™ cloud platform enables businesses to monitor and manage large, dispersed equipment fleets from anywhere, enhancing equipment performance and streamlining operations. Remote monitoring lets you remotely track equipment, measure performance, and receive critical warnings and alerts, resulting in maximized equipment uptime. Intuitive dashboards and reporting reduce service costs, improve equipment uptime, and automate regulatory compliance workflows.

RemoteIQ can monitor equipment on mobile devices and desktop computers at attended or unattended sites from anywhere in the world.
- View and control tank levels, line pressure, flow rates, and water quality for water and wastewater treatment plants, pump/lift stations, wells, or substations.
- Track the movement of high-value equipment fleets using GPS and geofencing.
- Monitor trends in railyard operations such as operator productivity, wheel slip, speed violation, and communication health.
- Optimize diesel engines, generators, compressors, or mobile equipment to manage autostart, speed control, throttling capabilities and run times.
Products
Security and Compliance
Advanced Security Protection for Connected Systems
SCADA systems are imperative in municipal and industrial markets that manage remote or unattended water and wastewater sites. However, with increased connectivity comes a greater risk to the safety and protection of these systems. It is crucial to implement strong security measures to prevent unauthorized access and protect against potential cyberattacks. The consequences of a breach could be catastrophic, causing significant financial loss, operational disruption, and even physical harm.
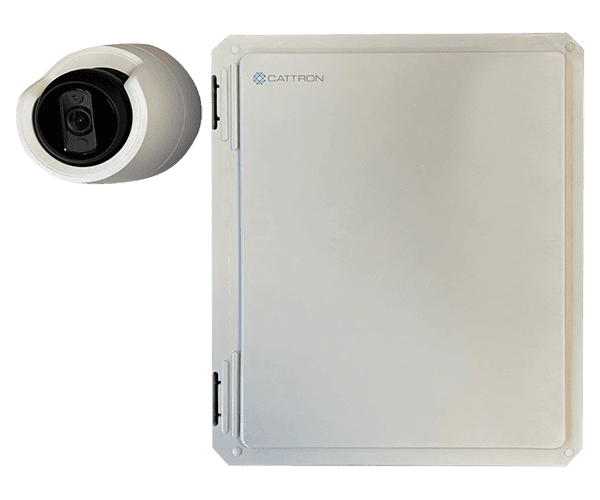
RemoteIQ™ Vision is an asset-based image capture camera solution for industrial, municipal, and commercial applications.
RemoteIQ Vision can be used as a complete standalone solution or with other Cattron products. It offers an optical snapshot of critical events happening at key assets. Having this third-eye approach to remote monitoring eliminates the need for on-site visits.
RemoteIQ Vision provides the following benefits:
- On-demand and scheduled snapshots are provided for remote fixed assets
- Day and night infrared illumination
- Alarm notifications via voice, text, or email
- Historical data is stored for up to five years on RemoteIQ
- Minimal data usage makes this a cost-effective solution
SCADA Solutions Security and Compliance
RemoteIQ™ applications that use the MQTT protocol have these added security measures in place.
Service Organization Control 2 (SOC-2)
SOC 2, or Service Organization Control 2, is a framework for establishing and ensuring the security, availability, processing integrity, confidentiality, and privacy of information within a service organization. For a SCADA system to achieve SOC 2 compliance, it needs to adhere to a set of Trust Service Criteria.
• TRUST SERVICE CRITERIA
• SECURITY – The system must implement measures to protect against unauthorized access (both physical and logical) and secure data from potential breaches.
• AVAILABILITY – The system must be available for operation and use as committed or agreed upon, ensuring that SCADA services are consistently accessible.
• PROCESSING INTEGRITY – The system processes must be complete, valid, accurate, timely, and authorized to ensure data integrity and system operations.
• CONFIDENTIALITY – Information designated as confidential must be protected from unauthorized access and disclosure.
• PRIVACY – The system must manage personal information by the organization’s privacy policies and comply with relevant privacy regulations.
Transport Layer Security (TLS)
Transport Layer Security (TLS) is a cryptographic protocol that ensures secure communication over a computer network, such as the Internet.
Secure Sockets Layer (SSL)
SSL (Secure Sockets Layer) for SCADA ensures secure communication by encrypting data exchanged between Supervisory Control and Data Acquisition devices, safeguarding sensitive information, and preventing unauthorized access.
Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) is a security mechanism that requires users to provide two or more distinct forms of identification before granting access, enhancing account security by adding an extra layer beyond traditional passwords.










